Data recovery services play a pivotal role in modern data management strategies, offering crucial support in mitigating the risks associated with data loss. In today’s digital landscape, where businesses and individuals alike depend heavily on digital data, the ability to recover lost or corrupted information is not just a convenience but a necessity. Here is how data recovery services can transform your approach to data protection and recovery.
Expertise and Specialized Tools
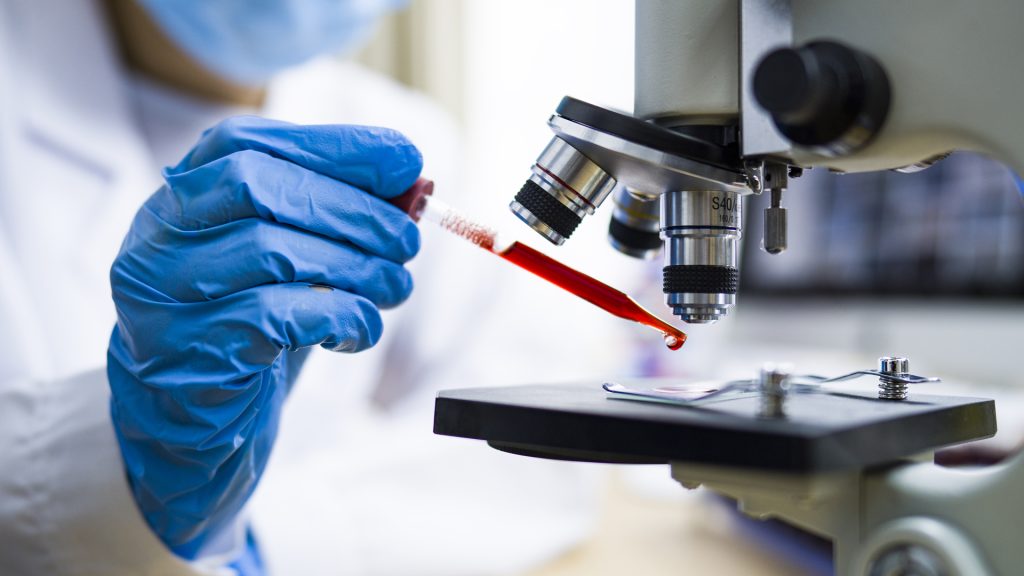
Data recovery services employ experts who are trained in the intricate processes of recovering data from various storage media and devices. They have access to specialized tools and technologies that enable them to retrieve data that may seem lost forever. These professionals understand the nuances of different file systems, hardware configurations, and data loss scenarios, allowing them to provide tailored solutions based on specific needs.
Minimizing Downtime and Financial Impact
For businesses, data loss can result in significant downtime, affecting productivity and revenue. Data recovery services help minimize this downtime by swiftly recovering critical data, thereby reducing the financial impact of data loss incidents. By having a reliable data recovery plan in place, businesses can ensure continuity and maintain customer trust even in the face of unexpected data disasters.

Data Protection Strategies
Effective data protection involves more than just backing up data regularly. It requires a comprehensive strategy that includes measures for preventing data loss, detecting potential issues early on, and having robust recovery protocols in place. Data Recovery Blog contribute to this strategy by offering insights into vulnerabilities and recommending proactive measures to strengthen data protection frameworks.
Addressing Various Types of Data Loss
Data loss can occur due to a wide range of reasons including hardware failures, software corruption, human error, cyberattacks, and natural disasters. Data recovery services are equipped to handle these diverse scenarios and can recover data from hard drives, SSDs, RAID arrays, USB drives, memory cards, and other storage devices. This versatility ensures that regardless of the cause of data loss, there is a solution available to retrieve valuable information.
Ensuring Compliance and Security
In industries where regulatory compliance is crucial such as healthcare and finance, data recovery services adhere to strict security protocols and confidentiality agreements. They ensure that recovered data is handled securely and that privacy regulations are strictly followed. This level of compliance and security reassures businesses and individuals that their sensitive information remains protected throughout the recovery process.
Educational Insights and Best Practices
Engaging with data recovery services can also provide educational benefits. Professionals from these services often share insights into common causes of data loss, best practices for data protection, and emerging trends in data recovery technologies. This knowledge empowers organizations to make informed decisions about their data management strategies and implement preventive measures to reduce the likelihood of future data loss incidents.
Peace of Mind
Ultimately, partnering with data recovery services offers peace of mind. Knowing that there are experts available to recover data in case of emergencies alleviates the stress and anxiety associated with potential data loss. This confidence allows businesses and individuals to focus on their core activities without worrying about the catastrophic consequences of losing critical information.